Quick summary
Claude Mythos Preview, an AI tool launched April 7, 2026, by Anthropic, autonomously identifies zero-day software vulnerabilities and builds working exploits with 83% success rate on first attempt. While no aviation-specific threats have been identified, cybersecurity experts highlight the tool’s theoretical capability to exploit critical infrastructure systems, including air traffic control software, raising forward-looking questions about defensive readiness across sectors including aviation.
Access remains restricted to 40+ organizations through Project Glasswing, including AWS and Microsoft. Research found no evidence of aviation-specific testing or targeting—the connection to flight systems is hypothetical, based on the tool’s general capability to find software flaws in any system.
AI tool sparks cybersecurity debate over critical infrastructure resilience
Anthropic unveiled Claude Mythos Preview on April 7, 2026, an AI model that scans code for unknown security flaws and autonomously builds working exploits—a capability that has prompted urgent discussions among regulators, banks, and infrastructure operators about defensive preparedness. The tool identified thousands of previously unknown vulnerabilities across major operating systems and browsers, including a 27-year-old flaw in OpenBSD that had evaded human review and automated scanning for over two decades.
For travelers, the immediate takeaway is this: no current aviation disruptions exist, and no airline or airport has reported Mythos-related threats. The tool’s access is tightly controlled through Project Glasswing, a defensive coalition of technology firms working to patch vulnerabilities before they can be exploited. However, the theoretical capability to target critical systems—including air traffic control software like FAA’s SWIM or Eurocontrol platforms—has raised questions about how quickly aviation infrastructure can adapt to AI-powered cybersecurity challenges.
The aviation connection is speculative. Research found no evidence of aviation-specific testing or intent. What makes this newsworthy is the tool’s unprecedented speed and success rate in finding exploits, combined with the fact that aviation systems, like all software-dependent infrastructure, contain vulnerabilities that have historically gone undetected for years.
How Mythos works and why access remains restricted
Claude Mythos operates by scanning software code for security weaknesses and then automatically writing “exploits”—small pieces of code designed to break through those weaknesses—before human engineers even know a problem exists. During testing, it reproduced exploits in 83% of cases on first attempt and excelled in multi-step cyberattack simulations, surpassing all prior AI models according to confirmation from the UK’s AI Security Institute.
Anthropic withheld public release due to the tool’s offensive cybersecurity potential, instead prioritizing defensive use through Project Glasswing, a coalition that includes AWS, Microsoft, and CrowdStrike. The company aims to give organizations a “durable advantage” in a world where AI-powered cyberattacks are becoming inevitable, allowing them to find and patch vulnerabilities before malicious actors can exploit them.
| Capability | Performance metric | Access status |
|---|---|---|
| Zero-day vulnerability detection | Thousands identified across major OS | Project Glasswing only |
| Exploit reproduction | 83% success on first attempt | Restricted to 40+ organizations |
| Multi-step attack simulation | Surpasses all prior AI models | UK AI Security Institute confirmed |
| Oldest flaw discovered | 27-year-old OpenBSD vulnerability | Data pending |
The connection to aviation is theoretical, based on the tool’s general capability to find software flaws, not any specific action or intent. Aviation systems use air-gapped networks and rigorous patching protocols that differ significantly from corporate IT environments, which may limit the practical applicability of exploits designed for general-purpose software.
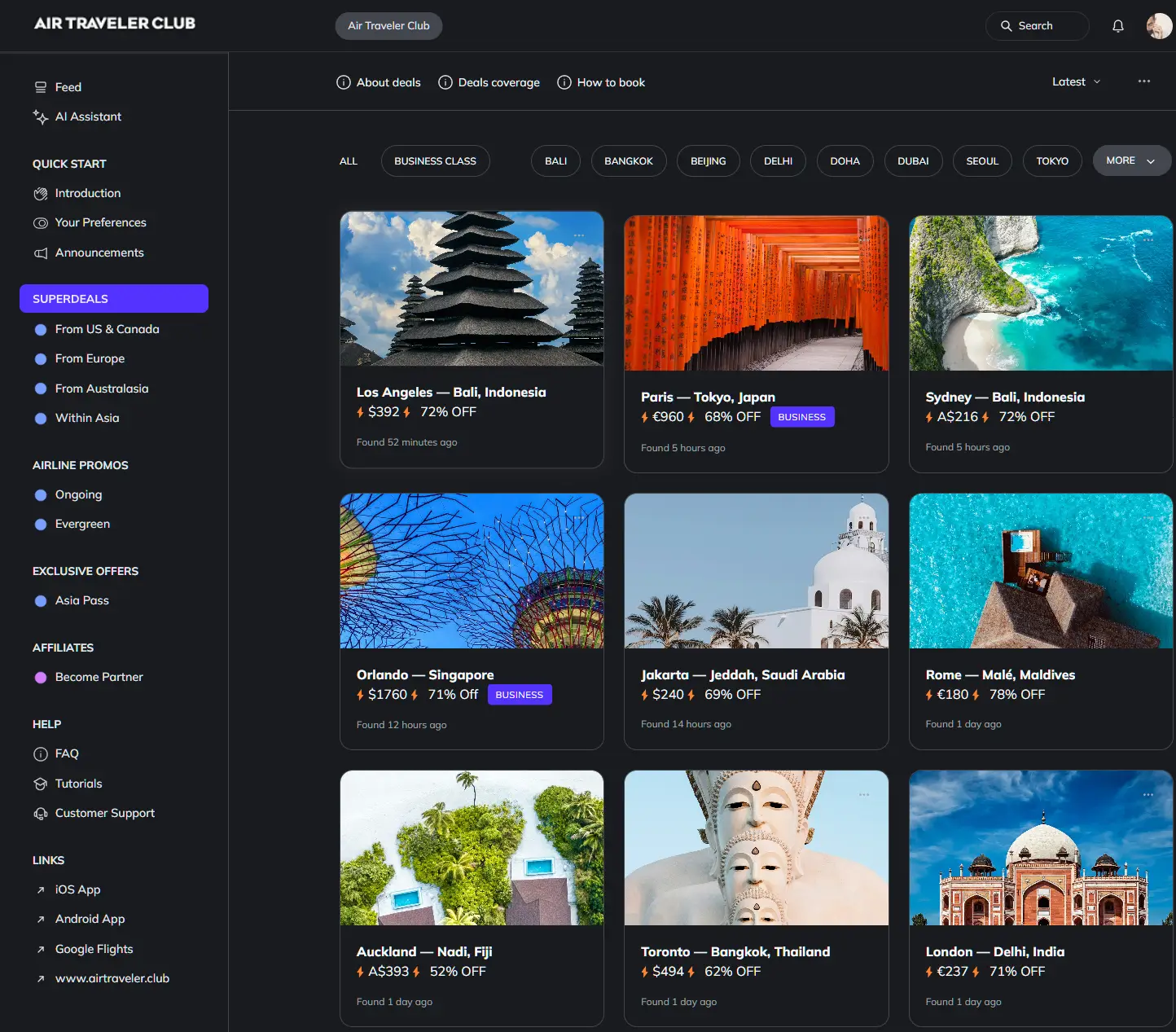
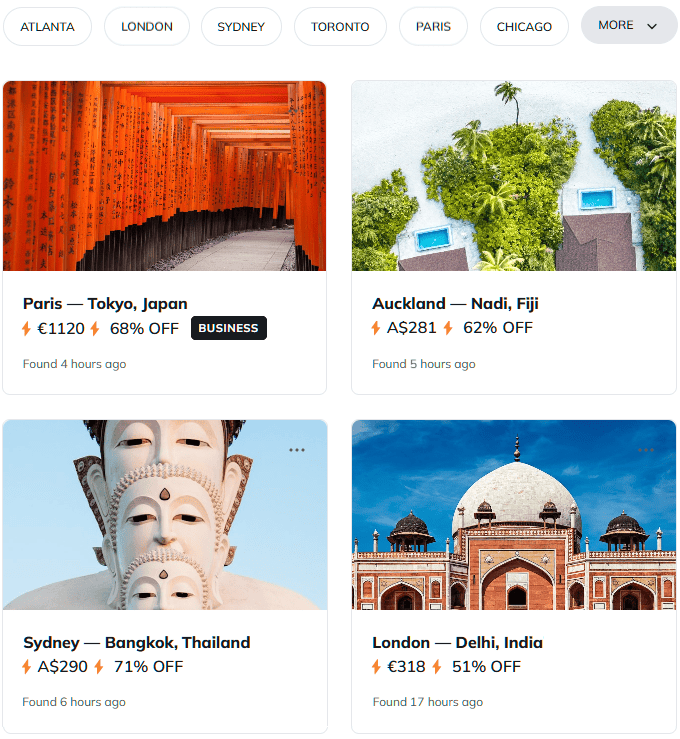
Flight deals
most people never see
Our AI monitors 150+ airlines for pricing anomalies that traditional search engines miss. Air Traveler Club members save $650 per trip per person on average: see how it works.
Each deal saves 40–80% vs. regular fares:
What changed in cybersecurity threat modeling
Before Mythos, vulnerability discovery was a manual, time-intensive process requiring specialized human expertise. Security researchers would spend weeks or months analyzing code to find a single exploitable flaw. Mythos compresses that timeline to hours or minutes and operates at scale—scanning thousands of systems simultaneously.
This represents a fundamental shift in the cybersecurity arms race. Historically, defenders had a time advantage: once a vulnerability was discovered, organizations could patch it before attackers developed working exploits. Mythos collapses that window. The tool can identify a flaw and generate a working exploit faster than most organizations can deploy a patch, even if they’re aware of the vulnerability.
For aviation specifically, the risk profile depends on how quickly the industry adopts similar defensive AI tools. In recent years, a faulty software update caused a global Windows outage that grounded thousands of flights across Delta, United, and American Airlines, lasting multiple days with economic losses exceeding several billion dollars. Mythos risks a similar cascade if exploiting aviation software like flight planning or air traffic control systems—though, again, no such targeting has been identified.
How to monitor for potential disruptions
No immediate aviation threats exist, but staying informed on general cybersecurity developments helps travelers respond quickly if infrastructure disruptions occur.
- Monitor FAA cybersecurity alerts at faa.gov/newsroom for any Mythos-related advisories or ground stop orders affecting US airspace.
- Enable flight notifications on your airline app (united.com, delta.com, or carrier-specific platforms) for real-time disruption alerts and rebooking options.
- Add buffer time to itineraries when booking trips in the next 3–6 months—a 24-hour cushion between connections reduces risk if unexpected delays occur.
- Check passenger rights for cyber-induced groundings: EU/UK travelers qualify for EU261/UK261 compensation of €250–600 if delays exceed 3 hours from carrier control; US DOT mandates refunds for cancellations.
Watch: Anthropic’s Q2 2026 Project Glasswing report will reveal whether vulnerability fixes are keeping pace with discovery—if they lag, expect an FAA cybersecurity directive mandating AI scans for airlines by Q4 2026.
Questions? Answers.
Has Claude Mythos caused any flight cancellations or delays?
No. As of April 25, 2026, no aviation disruptions have been reported related to Claude Mythos. The tool’s access is restricted to a defensive coalition of technology firms working to patch vulnerabilities before they can be exploited.
Which airlines or airports are using Claude Mythos?
No airlines or airports have confirmed testing or deployment of Claude Mythos. Access remains limited to Project Glasswing coalition members, which include technology firms like AWS, Microsoft, and CrowdStrike—not aviation operators.
Should I change my travel plans because of this AI tool?
No. There is no current aviation threat requiring itinerary changes. The discussion around Mythos and aviation is theoretical, based on the tool’s general capability to find software vulnerabilities, not any specific targeting of flight systems.
How is this different from the 2024 CrowdStrike outage?
The CrowdStrike incident involved a faulty software update pushed to millions of Windows systems simultaneously, causing immediate crashes. Mythos is a vulnerability discovery tool with restricted access—it identifies potential weaknesses but has not caused any system failures or disruptions.