Quick summary
European business travelers entering mainland China face mandatory device searches at borders, with authorities empowered to access corporate data, emails, and cloud accounts under the Cybersecurity Law amendment effective January 1, 2026. Exit bans—applied in civil and business disputes, not just criminal cases—can delay departure by months, inflating travel budgets 20-50% through legal fees and extended accommodation costs.
This applies to all European passport holders entering via Beijing, Shanghai, or any mainland airport from November 2025 onward. Corporate travelers carrying sensitive data should use burner devices. Those with unresolved business disputes should verify legal standing before booking.
European business travelers to China now operate under stricter enforcement of digital privacy laws and exit restrictions that can turn a routine trip into a months-long legal ordeal. The China Cybersecurity Law amendment, effective January 1, 2026, merged penalties for personal information violations and cross-border data transfers—fines now extend to forced closure of apps and websites. For travelers, this means border authorities have expanded legal grounds to search devices, demand cloud account access, and detain individuals carrying corporate data deemed sensitive under China’s National Intelligence Law.
Air Traveler Club’s January 2026 analysis of European government travel advisories shows no EU member state has downgraded China risk levels despite visa-free entry expansions. The UK Foreign Office, German Federal Foreign Office, and French Ministry for Europe maintain “exercise caution” warnings specifically citing arbitrary enforcement of local laws and digital surveillance risks. For business travelers on flights to China from Europe, this creates a compliance gap: visa-free entry simplifies arrival, but device hygiene and legal dispute verification remain mandatory pre-departure steps.
The €300-600 device strategy that protects corporate data
Business travelers carrying client lists, intellectual property, or confidential emails face a binary choice: accept device search risks or invest in clean hardware. The burner device framework—a factory-reset phone and laptop loaded only with essential apps—costs €300-600 upfront but eliminates exposure to China’s mandatory data cooperation laws. Under the National Intelligence Law (2017), Chinese authorities can compel companies to hand over data for state security purposes. This extends to foreign travelers whose devices connect to Chinese networks or cloud services.
The protocol: Purchase unlocked devices (€150-250 for a basic Android phone, €200-400 for a Chromebook or budget Windows laptop). Install only VPN software, messaging apps without chat history, and offline maps. Leave corporate laptops, work phones, and tablets at home. Store critical documents on encrypted USB drives accessed only after clearing Chinese customs. This two-day prep window adds logistical overhead but creates a clean digital footprint authorities cannot exploit.
For mid-level corporate travelers, the math favors burners. A single data breach—client information accessed during a border search, proprietary files copied by authorities—can trigger GDPR violations back in Europe. Fines under EU data protection law start at €20 million or 4% of global revenue. The €500 device investment becomes negligible insurance against regulatory exposure that could cost your employer millions.
Exit bans: The civil dispute trap European travelers miss
China’s exit ban system operates outside criminal law. Business disputes—unpaid invoices, contract disagreements, shareholder conflicts—can trigger travel restrictions without formal charges. European governments report cases where travelers were barred from leaving for months over civil matters their employers initiated. The 2026 Cybersecurity Law amendment tightened related penalties, creating legal grounds to detain individuals connected to companies under investigation for data violations.
The risk profile: Corporate executives, sales directors, and consultants working with Chinese partners face highest exposure. A Shanghai-based supplier files a commercial dispute in local court. Chinese authorities place an exit ban on the European signatory to the contract—even if that person is visiting Beijing on unrelated business. The ban remains until the dispute resolves, which can take 6-18 months in China’s legal system. During this period, the traveler cannot leave mainland China.
Financial impact: Extended stays inflate budgets by 20-50%. A planned 5-day trip becomes a 3-month ordeal. Accommodation costs alone: €80-150 per night × 90 nights = €7,200-13,500. Add legal fees (€10,000-30,000 for international representation), lost income, and emergency flights for family visits. Total unplanned costs: €25,000-60,000 per person. Travel insurance rarely covers exit bans, as they’re classified as legal matters, not medical or travel emergencies.
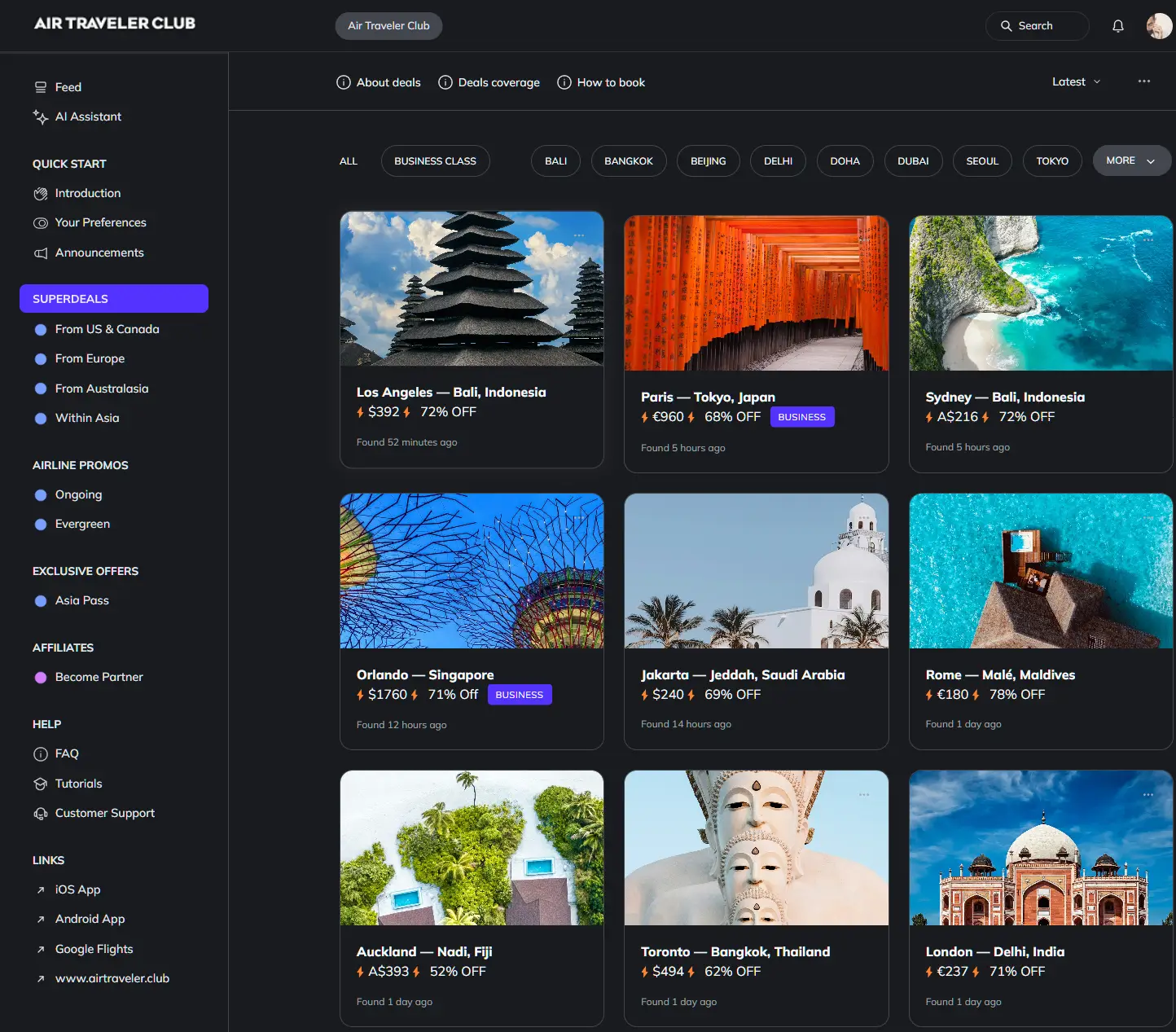
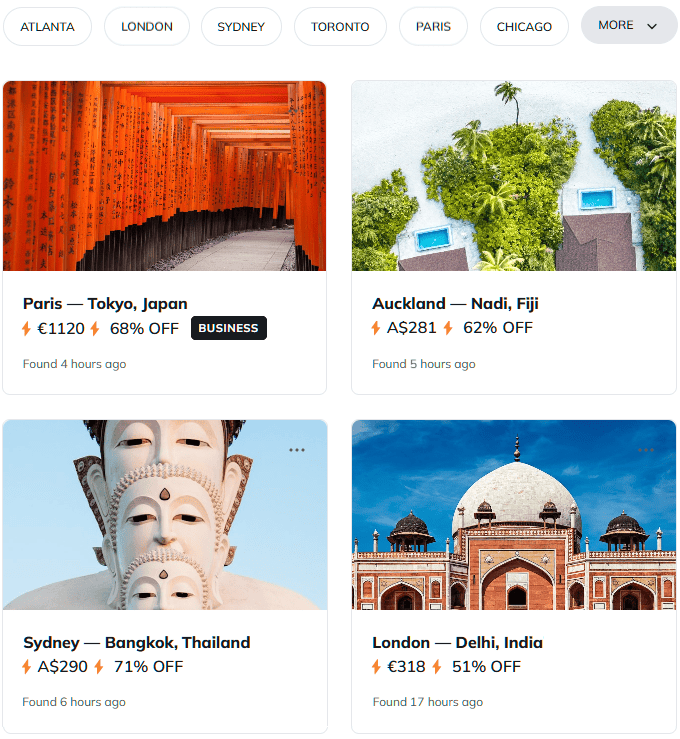
Flight deals
most people never see
Our AI monitors 150+ airlines for pricing anomalies that traditional search engines miss. Air Traveler Club members save $650 per trip per person on average: see how it works.
Each deal saves 40–80% vs. regular fares:
What the 2026 enforcement surge means for device searches
Chinese authorities conducted over 1,200 enforcement actions under the Personal Information Protection Law (PIPL) and Cybersecurity Law in 2025, targeting over-collection of data and illegal cross-border transfers. The 2026 priority: data leaks and breaches, with penalties escalating to business closures. For travelers, this translates to more aggressive border searches. Immigration officers now routinely demand phone unlocks, cloud account passwords, and laptop access—not just for suspicious individuals, but as standard procedure for business visa holders.
The technical reality: China’s border systems can clone device contents in under 10 minutes. Authorities use specialized hardware to extract chat histories, email archives, GPS location data, and app usage patterns. This data feeds into surveillance databases that cross-reference travelers against business registries, legal filings, and corporate affiliations. A European consultant carrying client contracts on their laptop creates a permanent record linking their employer to Chinese data systems—a GDPR nightmare if that data includes EU citizen information.
Why VPNs don’t solve the device search problem
Virtual Private Networks encrypt internet traffic but offer zero protection during physical device searches. Chinese border authorities don’t need to intercept your data in transit—they simply demand you unlock your phone and hand it over. The VPN app itself can trigger suspicion, as China bans unauthorized VPN use. Travelers caught with VPN software face questioning, potential fines, and extended detention while authorities verify the app’s purpose. The solution isn’t hiding your traffic; it’s eliminating sensitive data from devices entirely before you board the flight.
The GDPR trap: When your China trip violates EU law
European companies sending employees to China with work devices create cross-border data transfer violations. GDPR Article 44 prohibits transferring EU citizen data to countries without adequacy decisions—China lacks this status. When Chinese authorities search a laptop containing employee records, client databases, or HR files, that constitutes an unauthorized transfer to a third country. The company, not the traveler, faces liability.
The compliance framework: Employers must conduct Data Protection Impact Assessments (DPIAs) before sending staff to China with corporate devices. The assessment must identify risks (device searches, cloud account access, data retention by Chinese authorities) and implement safeguards (burner devices, data minimization, encrypted storage). Failure to document this process creates audit trails regulators use to impose fines. A 2025 case saw a German manufacturer fined €8 million after an employee’s work laptop was searched in Shanghai, exposing client contracts to Chinese authorities.
For solo business travelers and consultants: Notify clients before traveling to China with their data. Document the trip’s purpose, data minimization steps (burner devices, encrypted drives), and post-trip data deletion protocols. This creates a defensible compliance record if regulators investigate. The alternative—traveling with full corporate access on personal devices—exposes both you and your clients to GDPR penalties neither party can afford.
When the device strategy breaks down
Burner devices fail in three scenarios. First: Travelers who need real-time access to corporate systems for client meetings or deal negotiations. A clean laptop can’t access your company’s VPN, CRM, or shared drives without creating the exact data trail you’re trying to avoid. Second: Long-term assignments (3+ months) where maintaining two separate digital lives becomes impractical. Third: Industries where Chinese partners expect WeChat, Alipay, or other local apps tied to real identity verification—burner phones can’t pass these checks.
The workaround for scenario one: Cloud-based virtual desktops. Services like Amazon WorkSpaces or Microsoft Azure Virtual Desktop let you access corporate systems through a browser without storing data locally. You log in from the burner laptop, work in the cloud environment, then log out—nothing persists on the device. Cost: €50-100 per month for business-tier access. This adds expense but preserves the clean device principle while enabling real work.
For long-term assignments: Accept the risk or negotiate remote work arrangements that minimize China-based time. Some companies rotate staff every 60-90 days to avoid extended exposure. Others establish Hong Kong or Singapore offices as regional hubs, keeping sensitive operations outside mainland jurisdiction. These structural solutions cost more than burner devices but address the root problem: China’s legal framework fundamentally conflicts with European data protection standards.
Tourist vs. business traveler: The risk gap European advisories don’t explain
European government travel warnings lump all travelers into generic “exercise caution” categories. The actual risk profile splits sharply. Tourists visiting Beijing, Shanghai, or Xi’an for 7-10 days face minimal exit ban exposure—authorities rarely apply restrictions to individuals with no business ties. Device searches still occur, but the data at risk (vacation photos, personal emails, social media apps) carries lower stakes than corporate information.
Business travelers occupy a different threat landscape. Anyone traveling on a business visa, attending trade shows, meeting Chinese partners, or conducting site visits enters a legal environment where commercial disputes can trigger exit restrictions. The visa type itself signals to authorities that you’re engaged in economic activity subject to Chinese commercial law. This creates jurisdiction Chinese courts can exercise even if your employer is based in Frankfurt, Paris, or London.
The practical distinction: Tourists can reasonably travel with personal devices after basic precautions (factory reset, minimal apps, no sensitive photos). Business travelers should default to burner devices unless their trip involves zero commercial activity—a standard few corporate trips meet. The €500 device investment scales with risk: low for tourists, essential for anyone whose trip could generate legal disputes or data exposure.
Questions? Answers.
Do Hong Kong and Macau follow the same device search rules as mainland China?
No. Hong Kong and Macau operate under separate legal systems with different privacy frameworks. While both territories have increased surveillance measures, they don’t enforce mainland China’s Cybersecurity Law or National Intelligence Law. Border searches are less aggressive, and exit bans tied to mainland commercial disputes don’t automatically apply. However, data stored in Hong Kong can still be accessed by mainland authorities under national security provisions introduced in 2020.
Can Chinese authorities access my cloud accounts even if I use a burner device?
Yes, if you log into cloud services (Gmail, Dropbox, OneDrive) while connected to Chinese networks. Authorities can demand account credentials during border searches or compel service providers operating in China to hand over data. The safeguard: Don’t access cloud accounts containing sensitive data from Chinese IP addresses. Use offline storage (encrypted USB drives) or wait until you’ve left China to sync critical files.
What happens if I refuse to unlock my device at a Chinese border checkpoint?
Refusal triggers extended detention, potential device confiscation, and visa cancellation. Chinese immigration law grants authorities broad powers to deny entry or detain travelers who don’t comply with security procedures. In practice, refusal is interpreted as suspicious behavior warranting investigation. Most travelers who refuse unlock requests face 6-24 hour detentions while authorities verify their background, often resulting in deportation and future visa denials.
Are exit bans publicly disclosed, or could I be restricted without knowing?
Exit bans are not publicly disclosed. Travelers typically discover restrictions only when attempting to leave China—at airport check-in or immigration. Chinese courts don’t notify foreign nationals of pending exit bans, and European embassies have limited ability to verify ban status in advance. The only prevention: Conduct legal audits before travel if you or your employer have any